Information Security Classification Scheme
Information Security Classification offers a structured framework for managing information according to its sensitivity, ensuring that appropriate levels of confidentiality are consistently applied. This enables the University to implement proportionate security and compliance controls, protecting sensitive information while allowing greater flexibility for lower-risk data. The Information Security Classification documents were revised in April 2026, please see below.
Why is it important?
- Enhances the protection of sensitive data from breaches and misuse.
- Promotes compliance with applicable legislation and contractual obligations.
- Supports improved efficiency by standardising data handling.
- Supports a quick and effective incident response.
- Encourages secure collaboration within and beyond the organisation.
Information Security Classifications
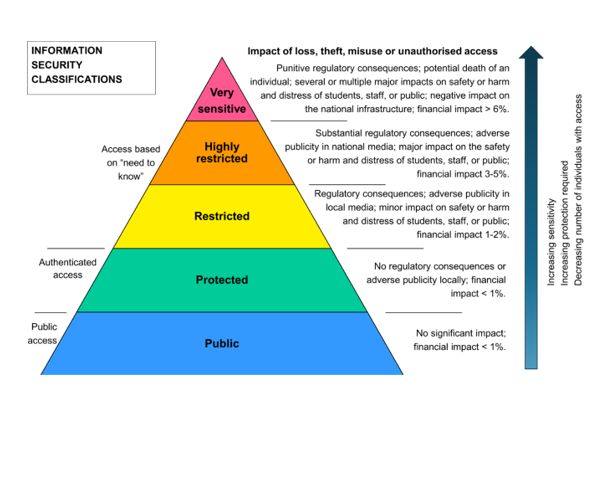
Diagram showing the different tiers of the information security classification scheme.
Information Security Classification, Ownership and Secure Handling Procedure
Further details of the Information Security Classification Scheme are set out in the documents below.
Information Security Classification, Ownership and Secure Handling Procedure
This procedure provides a clear framework for classifying University information by sensitivity and explains how staff should handle it safely to reduce risk and support secure, compliant working.
Information Security Classification Examples and Secure Information Handling Standard
Information Security Classification - Slide pack
We've also created a slide deck on Information Security Classification to help you better understand the topic in straightforward terms.
Key Updates
Key updates made in April 2026
- In response to user feedback, we have introduced an additional level called ‘Protected’.
- Updated the information handling documents renaming this to a standard and adding information for the new protected level.
- More references to other policies/guidance such as Acceptable Use, the AI Hub and AI TSS have been added and it has been made clearer how the classification relates to the Technical Security Standards.
- We are working with the Secure Research Environments Project on use cases - specifically for researchers.
How to
Information Security Classification is about thinking through what could go wrong if information was lost, shared inappropriately, or accessed by someone who shouldn’t see it. By considering the potential impact on individuals, the University, or our work, we can decide how much protection that information needs. More sensitive information needs stronger controls, while lower‑risk information can be handled more flexibly. Taking into account factors such as confidentiality, how the information is used, and where it’s stored helps staff choose the right classification and handle information safely and consistently in day‑to‑day work.
There are five information security classification levels.
- Very Sensitive
- Highly Restricted
- Restricted
- Protected
- Public
Factors which may intensify the impact - increasing the classification level - include:
- Timing: sensitivity can change over time e.g. information may have low sensitivity until processed or high sensitivity until published.
- Volume of data: e.g. a small dataset might be associated with a low potential impact but combining several such datasets can increase risk and raise the classification
- Context: e.g. data classification may be affected by related factors e.g. if information relates to someone at risk of physical harm or a topic of intense public or commercial interest.
- Mixed impact: When a set of information contains items with different classifications, the whole set must be classified at the highest level.
Your role in classifying information
Everyone who is authorised to use information is responsible for looking after it properly. Whether you access information through a system or receive it digitally, on paper or verbally, you must keep it secure. Please make sure you protect it to the level set by the Information Asset Owner and in line with the required security controls for its classification.
Before using any AI tools, always check that the information is appropriate to share and that you are following the classification and security rules.
If you are working on an activity that involves processing or sharing information then you may need to complete an Information Governance Risk Review (IGRR). This process helps to identify and mitigate risks so that the IGO can offer the right guidance and support.
For guidance on sharing and storing information visit Sharing and storing information | Information Governance Office | StaffNet | The University of Manchester and our staffnet page
Incident Reporting
If information is lost, stolen, damaged, shared with the wrong people, or accessed by someone who shouldn’t have seen it, please report it to the Information Governance Office as soon as possible at infosec@listserv.manchester.ac.uk.
Reporting issues quickly helps the University take the right legal and regulatory steps to limit any harm and reduce potential impact. This includes things that nearly went wrong, not just confirmed incidents.
You can find more information on how to report an incident here: Report data protection incident | Information Governance Office | StaffNet | The University of Manchester.
